Wi-Fi connections could be unsafe when there are suspicious connections to them. But how could it be possible for someone to know how many illegitimate connections are there. Or it might be possible that someone is eavesdropping or snooping through your Wi-Fi.
Such vulnerabilities may prove to be fatal as they could cause bandwidth swipe from a neighbor or a hacker to access your identity.
But, it’s never too late. You could follow some useful steps to ensure your wireless security that is easy as well as less time-consuming.
Here are seven effective steps we have gathered so that you could have a secure Wi-Fi connection.
1. Change the Manufacture name of your Wireless Network
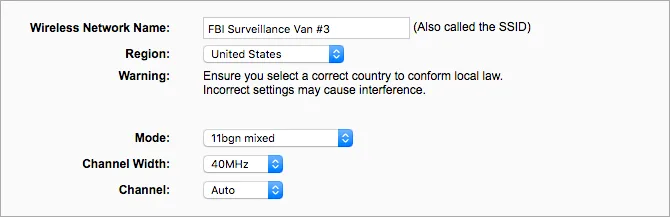
The most prior step towards security is to change the existing name of your Wi-Fi network or router, also known as Service Set Identifier (SSID).
Resetting the Wi-Fi name would be impactful in a way that a hacker could not easily guess the type of Router you are using. The manufacturer information could cater to the cybercriminal in knowing the weaknesses of that particular model you have and they could exploit them easily.
However, while changing the name you must keep in mind that the name should not contain your name for instance “Finn’s Wi-Fi”. Such Wi-Fi names make your connection obvious for the snooping eyes among all the others. Yet, the ones who include much personal information in their network names are prone to identity theft and cyber-attacks.
2. Create A Stringent Password for your Connection
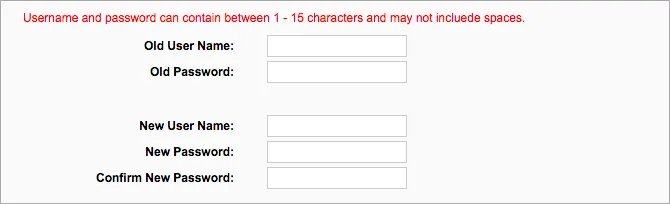
When you receive a wireless router, it already possesses a password that could easily be presumed by a data snooper, especially when he is familiar with the manufacturer of that device.
For protected strong passwords there is a uniform suggestion according to which it must be 20 characters long. With the combination of numbers and alphabets, the insertion of symbols makes it more difficult to be guessed.
Yet, very few people would know that there are websites such as RouterPassword.com and Default passwords. where default admin credentials could be searched through router models. This means it’s child’s play for a hacker to access your router if he knows the router model.
3. Enable Network Encryption Using WPA2 and AES
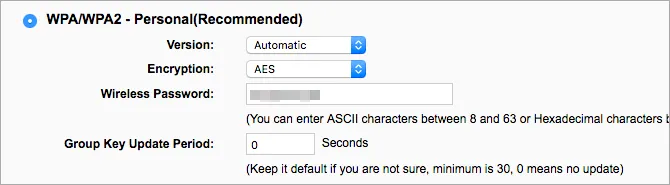
Encryption is a necessary tool for security purposes in all online deeds. Similarly, a router protected with encryption is difficult to access by an individual with malicious ambitions.
Enabling router encryption is a substantial feature that will take not more than 30 seconds of yours. Yet, you must look for WPA2 Personal mode while resetting and if it’s not available then you could use WPA personal. However, it is recommended not to use WEP mode which could be easily accessed.
The recent version of encryption i.e. AES should be selected after setting WPA2/WPA mode. However, the TKIP mode is not less secure yet AES is preferable because of its modern features. Also, people testing the combination of both AES and TKIP could fall prey to vulnerabilities. So, it’s better to remain with AES technology.
Finally, make a strong WPA2/WPA key on the password principles described above.
4. Enhance Firewall Protection

Like other devices and browsers, the routers also contain vulnerability holes that are necessary to identify and patch up. For such protections, a firewall helps to scan the incoming data and restricts the data which seems illegitimate and vulnerable.
However, many of the routers are pre-installed with firewall features such as the SPI firewall that allows the data after examining its legality.
Most probably the firewall protection is enabled by default but it is better to check if it is on. Yet, you could face some interruptions while playing online games. However, such issues could be resolved by heading on to Port forwarding.
Yet, you are advised to have added protections with the router firewall. These router firewalls sometimes become weak against vulnerabilities and unsafe data could get through it. Therefore, you must install antivirus software on your device to add a second layer of protection.
4. Disable WPS and UPnP
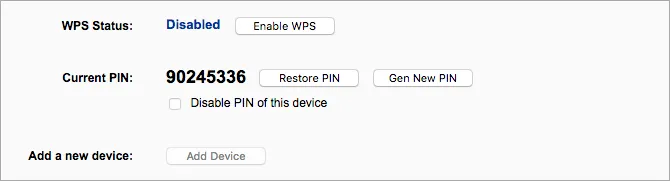
If the WPS (Wi-Fi protection features) is enabled then a new device could easily be added to your network. For disabling this feature you just have to press the WPS button on the router, then on the device, and voila which will establish the connection. After that, you must disable the WPS as it is easily cracked.
Universal Plug and Play (UPnP) make a newly connected device visible to the other devices on the network. Also, there are obvious security vulnerabilities and flaws to the UPnP design. Therefore, you must disable it as soon as possible.
6. Update the Router Firmware

Most of the time outdated software causes vulnerabilities to exploit. A software update is necessary a must privacy measure for all kinds of security flaws and data issues. Likewise, firmware, software that operates your router also needs to be updated.
Outdated firmware is risky as the pre-existing security loops could exploit and cause vulnerabilities. However, a new firmware could enhance security through extra features and improvements.
It is necessary to update your device regularly on a weekly or monthly basis. These updates could be downloaded from the router’s manufacturer website for which you should look for your model.
7. Disable Wi-Fi Connection When not in Use
A simplest but necessary preventive measure for security purposes is to disable your network connection when not in use. Such practice doesn’t give you much protection but it lessens the chances of malicious access to your Wi-Fi network.
Is Your Network Secure After These Security Modifications?
Many individuals think that such security measures couldn’t help much or they presume it as a long procedure. Yet, the protections for your wireless router mentioned above are rapid cures to avoid vulnerability exploitation.
Although, following these could not fully guarantee you the protection against strong and advanced malicious intrusions but makes it really difficult. Therefore, never leave your device an easy target for illegitimate access.
Share this article
About the Author
Zehra Ali is a Tech Reporter and Journalist. She has done her Masters in Mass Communication. Topics related to cybersecurity, IoT, AI, Big Data and other privacy matters are extensively covered by her on various platforms. You can follow her on twitter.
More from Zehra AliRelated Posts

15 Best Data Recovery Services and Software in 2024
KEY TAKEAWAYS Having reliable data recovery tools saves money, time, and reputation by allowing you ...
15 Best Free Phone Tracker Apps (Android – iPhone) In 2024
KEY TAKEAWAYS There are several phone tracking apps on the internet, with millions of users worldwid...
How To Get Free WiFi Anywhere With Privacy
Pack your backpacks with some free Wi-Fi gleaning tricks if you plan to travel. We constantly search...
Public Wifi Security – 10 Vital Steps For Data Protection
On the scale of all the important stuff that you use, on what number would you place your Wi-Fi conn...
6 Tips To Secure Your Home Wi-Fi Network Quickly
Within the confines of our own homes, browsing through the internet is as easy as ABC. As long as ou...

How to Setup Wireless Network for Your Mac Computers
If you have two or more Mac computers and you want to connect them to each other for fast and hassle...