DNS Hijacking, also known as DNS Redirecting or DNS Poisoning, is a strategy used by cyber pillagers. They trample upon a computer’s IP settings on the Internet to block access, restrict, and censor content.
By overriding a computer’s IP settings, the hijacker directs it to a rogue DNS server instead of the user-friendly domain names. This can also be achieved by monitoring and probing the traffic directly at imperative routing spots.
The Great Firewall of China, which the government uses to achieve Internet censorship in China, is the biggest example of DNS hijacking.
What is a Domain Name Service (DNS)
Domain Name Service is abbreviated as DNS. It is an Internet service that translates URLs such as Google.com to an IP address 8.8.8.8. Every website has an IP address linked to its URL via DNS. The DNS server holds a record of the IP address of every website along with the corresponding URL.
Here, the URL depicts the name and the IP address, just like a phone book holding records of the enlisted people with their addresses.
Many companies publish the website’s DNS address and an algorithm that keeps them updated simultaneously.
Your ISP (Internet Service Provider) and many other private business organizations operate the DNS system. Your computer is configured to use the ISP’s DNS server, but these settings can be changed manually.
DNS Hijacking – Mechanism
When you enter a URL into your browser’s address bar, it is sent to a DNS server to resolve into an IP address, mapping you to your friendly domain names. However, a wrong DNS server is often reached due to inadequate checks and balances.
An attacker might hijack the DNS, functioning between the computer and the DNS server, from a rogue device. If that’s the case, the hacker now owns the DNS server, as he might have changed the DNS settings and gained access to your computer.
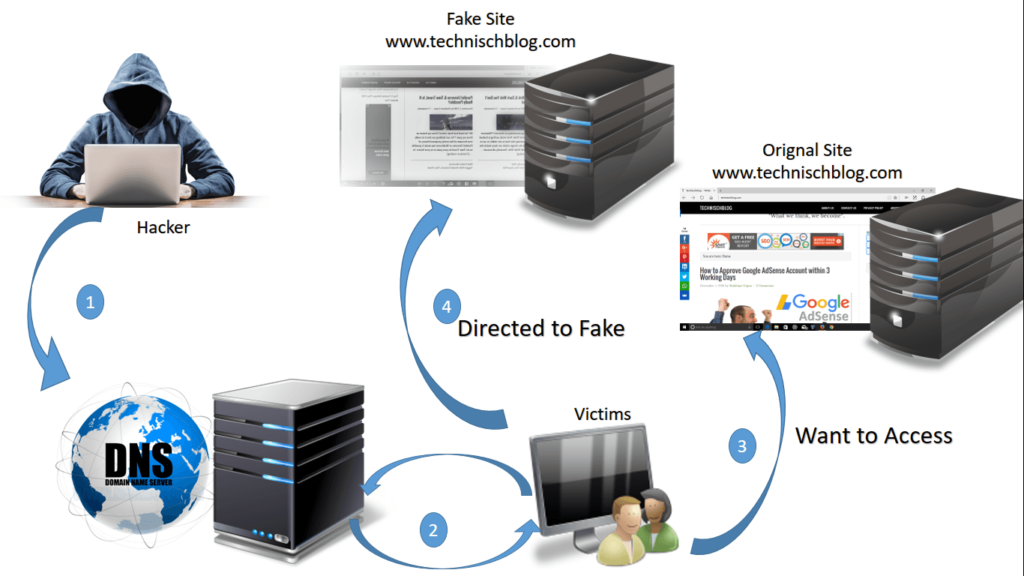
Now comes the point where the DNS server contaminates its records by swapping the IP addresses of the sites you wish to visit with those of another site that might be already infected with malware.
If an experienced hijacker carries out DNS hijacking, he might masquerade websites. As a result, he may compile sensitive information of users as well as the passwords and IP addresses of many websites.
In many cases, DNS hijacking is also carried out by using sophisticated malware such as a trojan horse. The DNS Changer trojan is a form of malware that profited about 14 million USD by hijacking the DNS settings of over 4 million computers through deceptive advertising revenue.
DNS Hijacking – Censoring the Internet
Many countries enforce Internet censorship, requiring Internet Service Providers to remove some specific domains from their DNS servers. However, this is a comparably easy form of hoodwinked censorship.
On the other hand, when a hijacker operates the whole network, he can restrict and block contractual DNS servers entirely or apply Deep Packet Inspection to block or misdirect requests specifically.
DNS Hijacking – Prevention
After discussing the dangers of DNS hijacking, we will share the easiest way to prevent it.
Domain Name System Security Extensions, abbreviated as DNSSEC, can be considered a DNS hijacking analysis used to verify the integrity of the DNS server and for protection purposes. DNNSEC minimizes the chances of a hijacker masquerading as a DNS, but unlike HTTPS in web servers, it is tough for a user to set up, validate, and monitor.
A good antivirus program can protect your computer against such attacks, but keeping it updated is essential.
DNS Hijacking – Fix
Strong privacy concerns are related to opting for the correct DNS server, as they will see each domain you try to connect to. You can change the DNS server to avoid censorship by your local Internet Service Provider. But eventually, this power will be withdrawn from the hands of your Internet Service Provider for a substantial cause.
You may change your DNS server to an autonomous DNS service like OpenDNS or Google DNS.
Different VPNs run their DNS servers, and if you connect to one of the VPNs, you can automatically use their servers. No one will be able to hijack your connection, and thus, your information will be well-protected. Such VPNs ensure that the sites you wish to visit resolve correctly and are not censored by the ISP or government.
Share this article
About the Author
Rebecca James is an IT consultant with forward thinking approach toward developing IT infrastructures of SMEs. She writes to engage with individuals and raise awareness of digital security, privacy, and better IT infrastructure.
More from Rebecca JamesRelated Posts
What is VPN Split Tunneling and How Does it Work?
Split tunneling is a VPN feature for anyone accessing foreign networks while connecting to their LAN...

What is VPN Encryption? It’s Types and Algorithims
Encryption is a method for enhancing the security and privacy of sensitive data or information that ...
Why is Opera VPN Not Working? How to Fix Opera VPN?
KEY TAKEAWAYS Opera VPN is a proxy service, not an actual VPN. That’s why it doesn’t wor...
VPN vs. Firewall vs. Antivirus: Which One is Better?
KEY TAKEAWAYS VPN, Antivirus, and Firewall are the most important tools to protect your online priva...

A Guide to Choosing the Right VPN for Downloading
How to hide downloading files from ISP? From the very start of the hilarious popularity of P2P file-...
What is Port Forwarding and How Does it Work?
Port Forwarding is a technique for redirecting computer signals between the local network and the In...


